RISK MANAGEMENT CLARITY
Risk Register vs Risk Assessment: Understanding the Key Differences
In modern risk management frameworks, organisations use several tools to identify, evaluate, and monitor risks that may affect strategic objectives, operations, and compliance obligations.
Two commonly used tools are risk assessments and risk registers. While closely related, they serve different purposes within the broader risk management process.
Understanding the distinction between these tools is essential for organisations seeking to build a structured and effective enterprise risk management (ERM) programme.
RISK ASSESSMENT DEFINED
What Is a GRC Risk Assessment?
A risk assessment is the process used to identify potential threats and evaluate their likelihood and impact.
Risk assessments are typically conducted during:
project planning
operational reviews
regulatory compliance exercises
security or safety evaluations
strategic planning processes
The objective of a risk assessment is to analyse uncertainty and determine the level of risk exposure associated with specific activities, assets, or decisions.
During a risk assessment, organisations typically:
identify potential risks
evaluate likelihood and impact
determine risk severity
prioritise risks for mitigation
Risk assessments may be conducted periodically or triggered by specific events such as organisational change, regulatory updates, or new operational initiatives.
RISK REGISTER DEFINED
What Is a GRC Risk Register?
A risk register is the central record used to document, monitor, and manage risks over time.
Once risks are identified through risk assessments or other processes, they are typically recorded in a risk register so that organisations can track them consistently across the enterprise.
A risk register usually includes information such as:
risk description
likelihood and impact scores
inherent and residual risk levels
assigned risk owner
mitigation actions
review dates and status
The register provides a structured overview of the organisation’s risk landscape, allowing leadership teams to monitor risk exposure and ensure that mitigation actions are implemented.
KEY DIFFERENCES
Key Differences Between Risk Registers and Risk Assessments
Although risk assessments and risk registers are closely connected, they play different roles in the risk management lifecycle.
| Risk Assessment | Risk Register |
|---|---|
| Evaluates potential threats | Records and monitors risks |
| Conducted periodically | Maintained continuously |
| Focuses on analysing likelihood and impact | Tracks risks, ownership, and mitigation actions |
| Often project or activity-specific | Provides enterprise-wide risk visibility |
| Produces risk analysis results | Maintains the ongoing risk record |
In simple terms: risk assessments identify and evaluate risks, while risk registers track and manage those risks over time.
MODERNISING RISK MANAGEMENT
How Risk Assessments and Risk Registers Work Together
In practice, risk assessments and risk registers are not separate processes but complementary components of enterprise risk management.
Risk assessments generate the information needed to understand potential threats, while risk registers provide the structured system used to manage those risks throughout their lifecycle.
For example:
A risk assessment identifies a potential cybersecurity vulnerability.
The risk is documented within the organisation’s risk register.
Mitigation actions are assigned to responsible teams.
Risk levels are monitored and reviewed regularly.
This integrated approach ensures that risks are not only identified but also actively monitored and managed over time.
FRAMEWORK ALIGNMENT
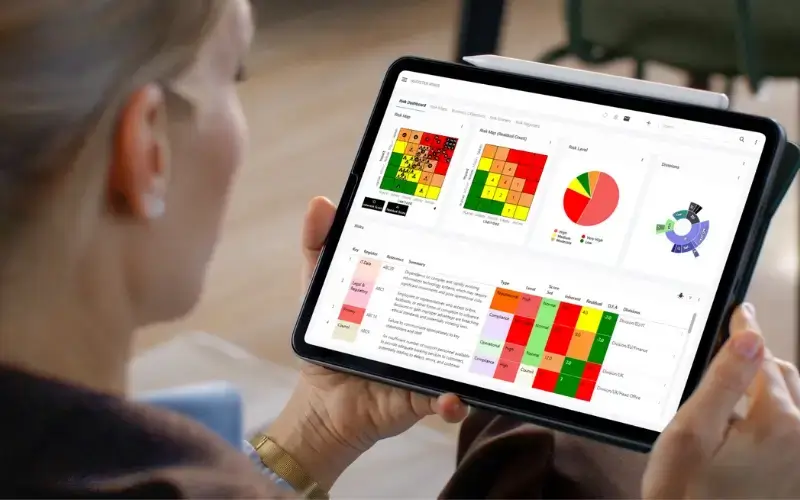
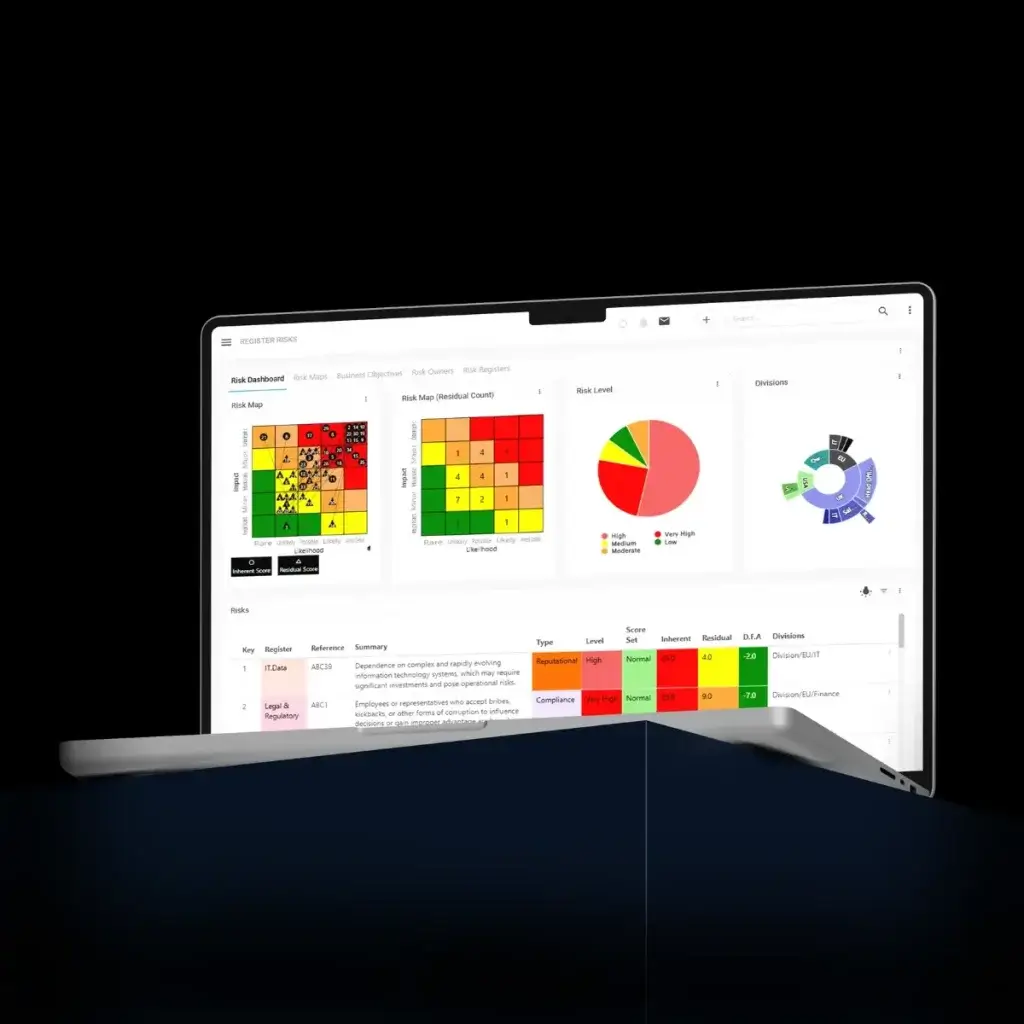
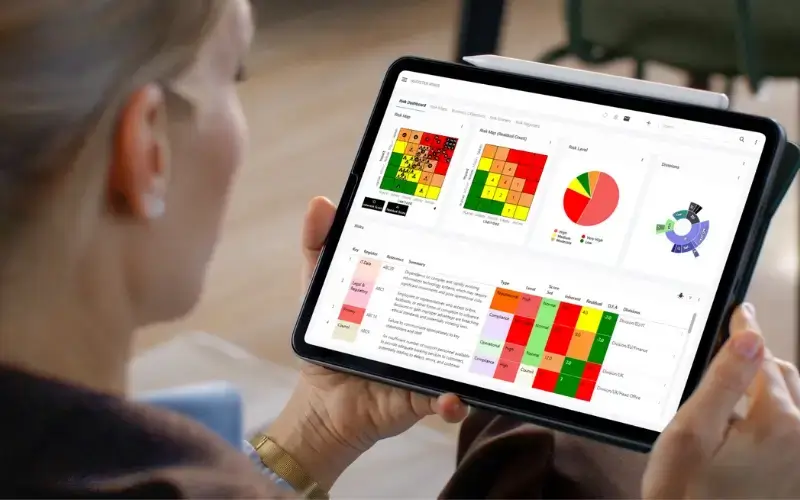
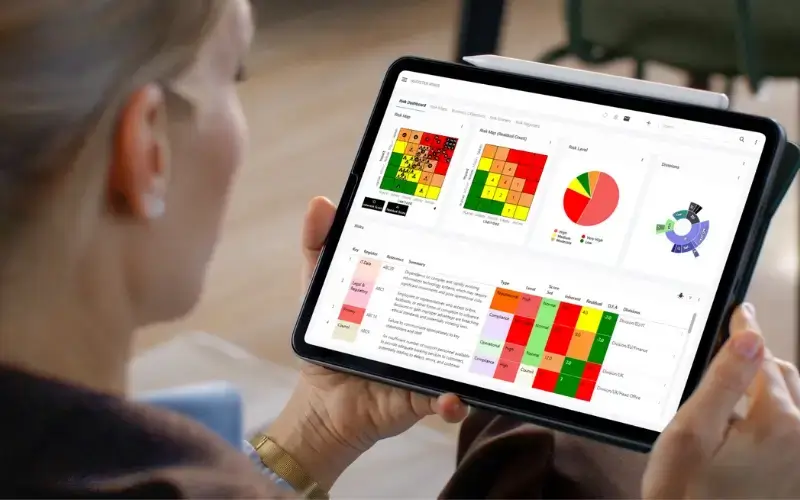
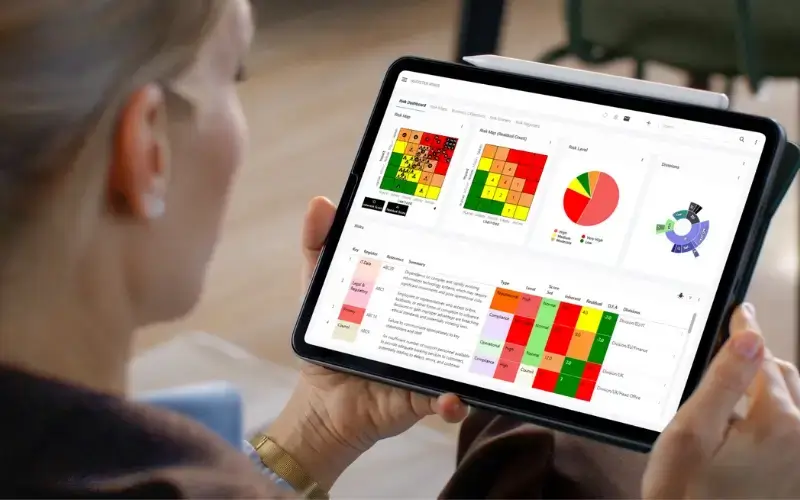
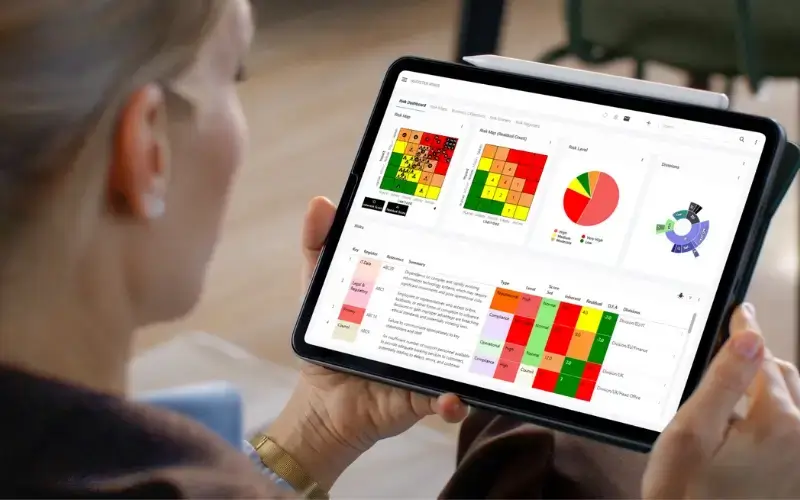
Why Modern Organisations Use Risk Register Software
While risk assessments and risk registers were traditionally managed using spreadsheets or manual documentation, many organisations now use dedicated risk register software to support enterprise risk management processes.
Risk register software allows organisations to:
centralise risk data across departments
automate risk scoring and monitoring
track mitigation actions and ownership
generate dashboards and heatmaps
maintain audit-ready documentation
Platforms such as Symbiant Risk Register Software enable organisations to connect risk registers with other risk management processes, including incident management, control testing, and structured assessments.
This creates a connected risk management system that improves visibility, accountability, and governance oversight across the organisation.
GOVERNANCE AND COMPLIANCE
Risk Registers in Enterprise Risk Management Frameworks
Risk registers play a central role in recognised governance frameworks, including:
ISO 31000 Risk Management
ISO 27001 Information Security Management
COSO Enterprise Risk Management
The UK Government Orange Book
Within these frameworks, risk registers provide the structured mechanism used to monitor risks, document mitigation actions, and support governance reporting.